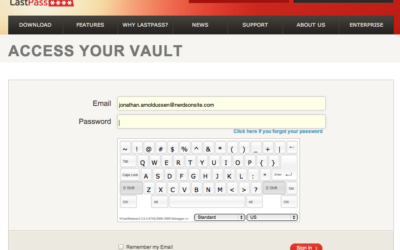
Remember the good old days when phishing schemes were easy to spot, at least to the trained eye? Errors in spelling or grammar, poor graphics, and general misuse of language were instant tip-offs. Those days are gone – modern phishing attacks are very sophisticated and very difficult to spot. Phishing pages are virtually indistinguishable from the genuine pages.
The un-targeted “shotgun approach” to phishihg is still increasing, but
the most dangerous phishing attacks are those that are targeted at specific companies, or even specific individuals. These are known as “spear phishing” attacks and are really blended attacks which combine social engineering attacks with information gathering and reconnaissance.
In a typical scenario, the attacker will use publicly available information, Google hacking methods, phone calls, “dumpster dives”, and even on-site reconnaissance to gather information about the structure of a company, the relationships between employees, email addresses, direct phone numbers, etc., for use in targeted attacks. It is surprisingly easy to obtain a large amount of information about a company this way.
The attacker then uses this information to target specific individuals. We associate familiarity with trust, so a message that contains personal information and details that would normally be known only to our co-workers lowers our defenses. For instance, an attacker may craft an email, with a forged address to an executive which references the fact that a coworker is on vacation in a specific location and asked to have a particular file sent. An attacker might also send a friendly note to an administrative assistant that contains personal information about his/her family, current events within the company, and so on. This message might contain a link to a malicious file that exploits a recent vulnerability in a web application. The victim has no idea that there has been a compromise.
We can imagine just how powerful these attacks can be. They do require a considerable investment of time and energy, so they are reserved for targets with known valuable information assets. Who does that include? At one end of the spectrum is any company that stores enough information about its employees or clients to facilitate identity theft (that includes a LOT of small businesses). Who is at the other end of the spectrum? How about the dozens of embassies and NGOs that were the victims of the recently-discovered Chinese “GhostNet” ? Targeted phishing attacks are suspected to be the attack vector used for most of these infiltrations.
How do companies defend against spear phishing attacks? Information protection policies and filtering at the gateway can mitigate the risks somewhat, but the most important line of defense is education and user awareness. We understand the threats against our physical assets and take reasonable precautions to protect them. We lock our doors, install alarms on our cars, and avoid dark alleys at night because we know that there are thieves who want to steal from us.
When it comes to information theft, the threats less familiar and the safeguards are less understood. As a society, we are just beginning to understand that information has become a currency that has a very real monetary value.
BOTTOM LINE: As consultants, it is our RESPONSIBILITY to help ALL of our clients understand the the VALUE of information, the THREATS they face, and the PRECAUTIONS that will must take to protect valuable information.
Dennis H in West Virginia, US
April 7
What Is Smishing (And How To Protect Yourself)
Smishing is a new form of phishing that uses text messaging instead of email. It’s a growing problem worldwide,...