Smishing is a new form of phishing that uses text messaging instead of email. It’s a growing problem worldwide,...
Nerds On Site North America
Nerd Resources

CloudFlare Bug Potentially Exposes Private Information
Nerds Hosting uses CloudFlare to power certain aspects of our hosting infrastructure, and thus we felt it important to...
Identity Theft Tactics – be aware and protect yourself
Identity Theft is a horrible experience to go through. Just ask anyone who has been victimized. It can takes many...
Do you have one of the 80 million unsecured routers?
In the midst of all the security alerts you and we receive on a regular basis, this one stands out and you can and...
Peekaboo I See You – how to privatize your Internet cameras
Here is a map of Trendnet Webcams that were/are publicly viewable by anyone in the world with an Internet connection....
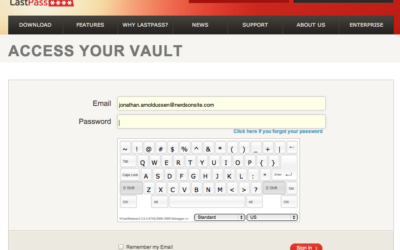
Securely Accessing your Passwords in an Internet Cafe
On a recent trip, I had a sudden emergency need to access a critical system back home, but I didn't have any computing...
Wireless Networks Compared: Europe vs. North America
I recently returned from a trip to Western Europe, and was surprised by the state of their WiFi networks. Now, to be...
Tired of password breaches yet? 5 steps to Peace of Mind
With the most recent password breach at Yahoo barely a month since the LinkedIn password leak, it seems a regular...
Macs are not as secure as we thought
If you own a Mac, chances are you've always had a good deal of comfort as it relates to the security and...